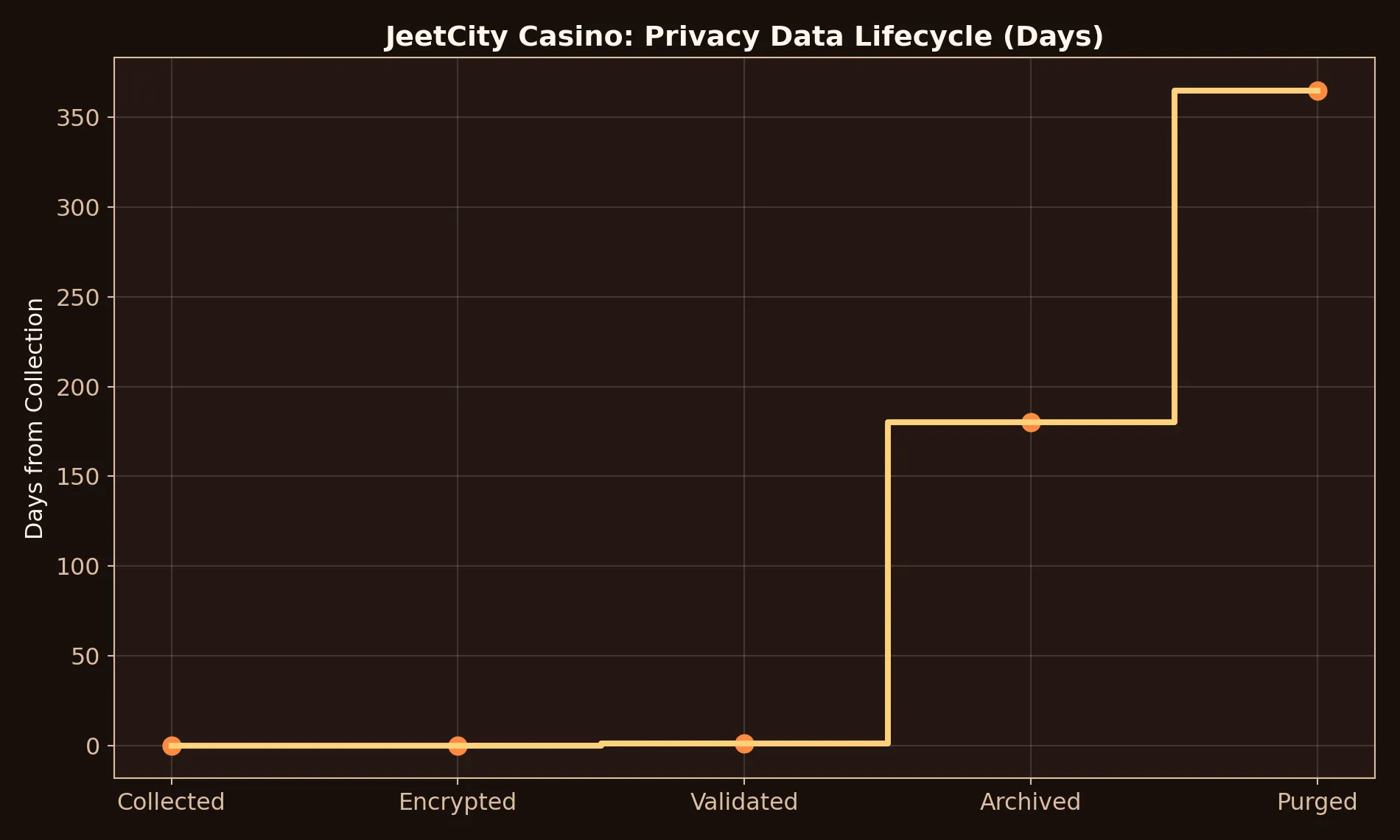
This lifecycle chart visualizes how data moves from collection to retention and cleanup. It turns abstract privacy language into an operational timeline you can understand quickly. Use it to see where control points and safeguards matter most.
Clear privacy notes on how we handle reader submissions, review evidence, and retention controls while covering JeetCity Casino in a security-first editorial workflow.
We only collect what is needed to answer support-style queries and improve review quality. That usually means message content, optional contact details, and context needed to understand payout or bonus issues. We do not ask for unnecessary identity documents on this site, and we avoid storing sensitive files unless absolutely required for a specific dispute walkthrough.
Records are retained for a limited period to maintain continuity on unresolved cases and to improve future guidance. Old data is either archived with reduced identifiers or removed based on relevance and legal obligations. Retention exists to preserve evidence quality, not to build profile depth on readers.
Only authorized reviewers handling support and editorial operations can access case notes. Internal access follows a need-to-know model, reducing unnecessary exposure. We encourage users to redact card digits, full IDs, and unrelated personal details before sharing screenshots. Better redaction improves both security and review speed.
We do not sell reader data. Information is shared externally only when required for dispute handling or legal compliance, and only to the extent necessary for that purpose. Where possible, we use summaries instead of full records. This keeps context useful while reducing personal data surface area.
If something in your submitted record is inaccurate, ask for correction and include the exact update. If you want data removed, request deletion with enough context for reliable identification. We process these requests in a reasonable timeframe and confirm outcomes clearly.
Before sending evidence, remove unnecessary personal fields and keep only transaction-relevant details. Use one clean thread, avoid forwarding sensitive files multiple times, and store your own local copy of communications. Privacy quality improves when both sides follow disciplined evidence hygiene.
Most privacy leaks happen during rushed evidence sharing, not from the original dispute itself. Before sending any screenshot, crop out unrelated tabs, full card numbers, full addresses, and unnecessary personal identifiers. Keep only transaction IDs, timestamps, cashier states, and game-round references. This preserves case usefulness while reducing exposure. For JeetCity or any other brand, support usually does not need your full document context to verify a payout timeline. A privacy-first screenshot still works when it is focused on the exact operational detail under review.
Readers should also maintain a small local archive with disciplined retention rules. Save only what helps future verification: key tickets, payout confirmations, and terms snapshots tied to active bonuses. Delete stale duplicates and avoid forwarding the same files through multiple channels. A compact, clean record set is safer and easier to navigate during disputes. This page is intentionally long because privacy is not one toggle; it is a chain of habits. When each habit is applied consistently, you get both better security and faster support interactions, which is exactly what disciplined players need in high-variance environments.
Many Australian readers use offshore brands, which means data may pass through multiple compliance and hosting environments. That does not automatically mean unsafe, but it does raise the value of disciplined self-protection. Share only what is necessary for the exact support step, verify recipient channels before uploading files, and keep your own redacted archive. If a platform asks for additional verification, ask why each document is needed and which stage it closes. This habit keeps control in your hands and reduces over-disclosure. Privacy confidence comes from repeated small decisions, not from one checkbox in an account settings screen.
This chart is generated for this page only and uses the same brand palette as the main review to keep visual consistency across the full site.
This lifecycle chart visualizes how data moves from collection to retention and cleanup. It turns abstract privacy language into an operational timeline you can understand quickly. Use it to see where control points and safeguards matter most.
